Two-factor Authentication with UA Single Sign-On
see also: UA VPN using 2FA
Two-factor authentication requires users to provide a "second factor" in addition to the correct password to authenticate and gain access to resources. If your password is "something you know", the second factor can be described as "something you have" such as your working telephone or smartphone. [In principle the second - or third - factor could be "something you are" such as fingerprint or voiceprint recognition.]
The UA Identity Provider has been extended to allow use of two-factor authentication using Duo Security. When two-factor authentication is invoked (as described below) you will first provide your identifier and UA Password just as you usually do for most applications. Some services will soon require use of 2 factor authentication. You can opt in to use of 2 factor authentication by logging in to ELMO, https://elmo.alaska.edu.
What does the user experience look like for 2 factor authentication to web services?
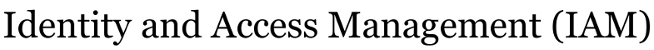
Once your identity is flagged for 2 factor authentication, your first access of one of the relying services triggers a login screen requesting your UA Username and UA Password (figure 1A). Your UA Username and UA Password are verified against UA’s directory service (never exposed to the service itself). Once verified, you will be prompted to provide a second factor – something you have (figure 1B). Assuming you use the recommended option “Send Me a Push”, you will need to accept the request pushed to the Duo app on your smart phone (figure 1C).
A one-time registration process records a user's phone number and preferred means of providing the second factor. That is, the initial registration associates a specific phone number and mode of communication with your UA Username or ID #. A single user may have multiple registered second factors; for example, you might have a smartphone that uses the Duo Security app and a land line on which you can receive a voice call providing a one-time code.
When you access other relying services during the day from the same browser on the same computer, you will not be prompted to authenticate again.
If you access any of the relying services in a different browser (use a different web browser on the same computer, or use a different computer) you will need to re-authenticate because the new browser does not have the information that you have authenticated.
Which other services participate in SSO and will not require additional authentication? A list of about 50 services relying on SSO via the UA Identity Provider is at: https://iam.alaska.edu/trac/wiki/IamUaArp#Services Other research and scholarship services are potentially available as well if they participate in the InCommon federation. A list of 250+ “partners” that provide information services to higher education is at https://www.incommon.org/participants/ .
Why is UA deploying 2 factor authentication? What is the benefit?
Second factor authentication mechanisms provide greater assurance of correctly identifying users and preventing abuses when someone’s username and password are compromised. Federal guidelines for agencies require 2 factor authentication in cases where a compromise could entail “moderate” inconvenience or distress or damage or financial loss or liability or if there is “any” risk of unauthorized release of sensitive information. Like most institutions, UA increasingly relies on web-based applications, which are primary targets of exploits. Many attacks (a Verizon summary of breaches states 95%) involve harvesting credentials from end user devices, then using them to log into web services. For example, CU Boulder potentially experienced a compromised emergency system during a police incident resulting in several false active-shooter reports. Boston University implemented 2 factor authentication after compromised passwords enabled employee payroll deposits to be diverted.
Are other Universities using 2 factor authentication? Are they using Duo Security?
Yes and yes. Many institutions have adopted 2 factor authentication and require its use to access key institutional services. Some require use by all employees and at least one (Virginia Tech) requires use by both employees and students. Over 100 Universities have agreements with Duo; several of them have very large implementation with many thousands of users.
Which identities use Duo 2 factor authentication?
Participation at UA is being gradually deployed. Users that have an attribute in their UA Active Directory record indicating use of 2 factor authentication will automatically be presented with the auto-enrollment process (see Duo 2FA Enrollment Guide for UA DuoUAenroll) the next time they log in to any of the services that rely on our SAML (Shibboleth) SSO.; after that, they will be challenged for 2nd factor to authenticate. For now, users contact IAM and request 2 factor authentication. A service owner may require users to be enrolled in 2FA to access that service.
What services or which identities require Duo 2 factor authentication? DocuSign (electronic signatures), Amazon Web Services administrator access, and RAVE emergency communications are the first services at UA being configured to require 2 factor authentication. Other services may require 2 factor authentication if and when service owners determine it is appropriate. Users who have not enabled 2 factor authentication will not be able to access these services until they opt in to 2 factor authentication for their UA identity.
What if I do not have or decline to use my smartphone as 2nd factor?
You may enroll other types of devices either as backup or alternatives to a smartphone:
• any telephone number to receive a call from Duo that will prompt for a response; or • a small USB token from YubiKey;
The experience of many thousands of users suggests the smartphone app is almost always the most convenient and least obtrusive mechanism, but you are encouraged to enroll other devices in case your smartphone is unavailable.
How do I opt in to to use Duo 2nd factor for logins using my ID?
You can opt in to use of 2 factor authentication by logging in to ELMO, https://elmo.alaska.edu and choosing to "Opt In" to Duo MFA.
Once I opt in, how do I Enroll and configure my phone or other second factor?
If your authentication invokes two factor authentication (because a service requires it or because you are in the security group using two factor) and you have not previously used Duo Security with UA, you will be presented with a page to automatically enroll and designate your phone number to be used for second factor. Step-by-step directions are here:
Duo 2FA Enrollment Guide for UA DuoUAenroll
Users can enroll and configure devices in the Duo Self Service Portal
Users may manage or add managed devices for second factor authentication in Duo's Self Service Portal. AFTER successful initial authentication to any service, users may checking the "Manage devices" button instead of the Log in > button. This will trigger a second factor authentication to one of your existing devices; upon successful submission of the second factor, users will see a control panel like the following:
Attachments
-
2nd factor login.png
(28.7 KB) -
added by dabantz@… 11 years ago.
IdP_second_factor_login_screen
-
Duo_app_login_request.png
(59.3 KB) -
added by dabantz@… 11 years ago.
Duo_mobile_app_login_request
- 2nd factor login.jpg (38.8 KB) - added by dabantz@… 11 years ago.
- Duo_app_login_request.jpg (33.8 KB) - added by dabantz@… 11 years ago.
- PoC installation steps.pdf (118.3 KB) - added by dabantz@… 11 years ago.
-
Duo_login.png
(35.6 KB) -
added by dabantz@… 11 years ago.
Duo second factor request on UA IdP login
- Manage_portal.png (33.9 KB) - added by dabantz@… 11 years ago.
- Enroll_device.png (40.2 KB) - added by dabantz@… 11 years ago.
-
2FA user experience.png
(90.3 KB) -
added by dabantz@… 9 years ago.
2FA login screens (Figs 1A, 1B, 1C)
-
2FA_user_experience.png
(90.3 KB) -
added by dabantz@… 9 years ago.
2FA login screens (Figs 1A, 1B, 1C)